In an era where data breaches continue to pose significant threats, safeguarding sensitive information is paramount. Startling statistics reveal the urgency of securing online communication.
In the first quarter of 2023 alone, over six million data records were compromised globally due to data breaches. Notably, the fourth quarter of 2020 saw the highest number of exposed data records.
Nearly 125 million data sets were compromised since the first quarter of 2020. Against this backdrop, ensuring the integrity of SSL certificates becomes crucial.
In today’s guide, we walk you through how to check SSL certificates using OpenSSL in Linux and Windows environments. At the end of this guide, we hope you will be fortified with the knowledge to strengthen your digital defenses.
What is an SSL Certificate?
SSL (Secure Sockets Layer) certificates foster secure communication between websites and users. Acting as a trust indicator, these digital certificates guarantee the websites’ reliability and safeguards data confidentiality during transmission.
They encrypt sensitive information to instill confidence and protect users against unauthorized access to ensure a safe online experience. SSL certificates come in various types. Each of them offers different levels of validation and trust. The most common SSL certificate types include;
- Domain Validated (DV) Certificates: Domain Validated (DV) certificates are the most basic type of SSL certificate, and they offer a fundamental level of security. They are also typically the most affordable option. To obtain a DV certificate, the certificate authority (CA) verifies only the ownership of the domain. DV certificates are best suited for personal websites, blogs, or small businesses where encryption is the primary concern.
- Organization Validated (OV) Certificates: Organization Validated (OV) certificates provide a higher validation level than DV certificates. In addition to verifying domain ownership, the CA conducts a more thorough vetting process, verifying the organization’s identity and existence. This involves confirming the organization’s legal registration, physical address, and phone number. OV certificates display the organization’s information in the certificate details, assuring visitors they are accessing a legitimate website. OV certificates are best-suited for e-commerce platforms. They’re also suited for corporate websites and other business-critical websites where user trust and identity verification are essential.
- Extended Validation (EV) Certificates: Extended Validation (EV) certificates offer the highest level of validation and instill the most trust in visitors. The CA performs a rigorous verification process. This includes running legal, physical, and operational checks, to confirm the identity and legitimacy of the requesting organization. Websites with EV certificates display a secured padlock along with the organization’s name when you click on a padlock, in most browsers. This highly visible indication of trust gives users a visual cue that they are interacting with a secure and legitimate website. EV certificates are commonly used by large corporations, financial institutions, and e-commerce platforms where establishing maximum trust is critical.
There is also the single domain, wildcard SSL certificate along with multi-domain SSL certificates, which provide flexibility for securing multiple subdomains or domains with a single certificate.
And, what is OpenSSL?
OpenSSL is an indispensable open-source software toolkit for implementing SSL/TLS protocols. Its versatility extends to Linux and Windows.
This makes it accessible to many users. With OpenSSL, you gain access to a powerful command-line interface for seamless execution of cryptographic operations.
From securing connections to verifying SSL certificates, OpenSSL is the tool of choice. Here’s a summary on how to check SSL certificates with OpenSSL;
A. Checking SSL Certificates with OpenSSL in Linux Systems
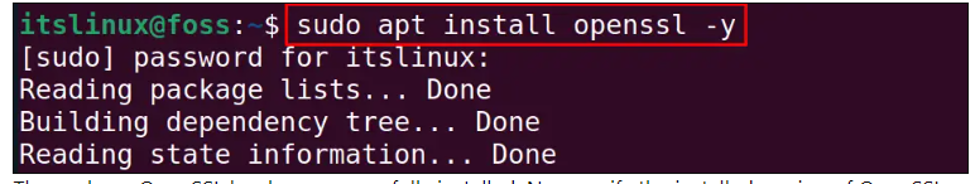
You will need to first, install OpenSSL. The installation process may be different depending on your Linux distribution system.
You don’t even need to worry though. The process generally involves using package managers like apt or yum. Here are the steps for popular distributions like Ubuntu and CentOS.
Ubuntu:
- Step 1: Open a terminal window.
- Step 2: Run the command: sudo apt update. This will update the packages of Ubuntu.
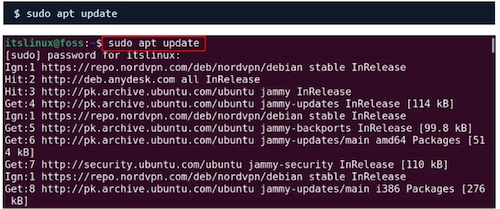
- Step 3: Run the command: sudo apt install openssl. This will install the package.
CentOS:
- Step 1: Open a terminal window.
- Step 2: Run the command: sudo yum update –y
- Step 3: Run the command: sudo yum install -y openssl
Here are some essential commands to check SSL certificates;
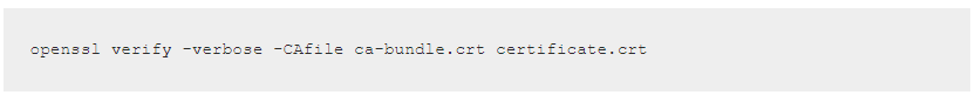
- To view certificate information, run the command below:
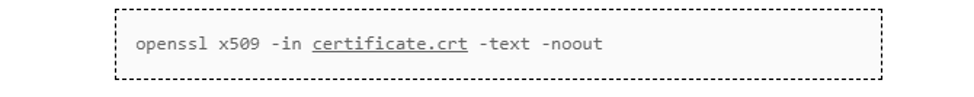
- To ensure the certificate chain is valid and trusted, use the following command:
You may run into issues when checking SSL certificates. This is normal though, so don’t fret. Here are some good troubleshooting tips to unstuck:
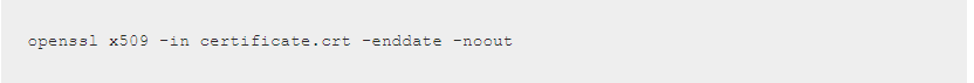
- Certificate Expiration: Below is the command for checking the expiration date of a certificate. If the certificate is nearing expiration, renew it.
- Revoked Certificates: Use Online Certificate Status Protocol (OCSP) checks. You can also use the Certificate Revocation Lists (CRLs) to determine if a certificate has been revoked.
- Generating Private Keys and Certificate Signing Requests: OpenSSL offers functionality beyond certificate checking. You can generate private keys and create certificate signing requests using OpenSSL commands, adding to its versatility.
B. Checking SSL Certificates with OpenSSL in Windows
Note that even for Windows; the first step is installing OpenSSL. Here’s a small twist: Windows do not natively support OpenSSL.
That shouldn’t stop you from checking your certificates anyway. You can obtain the Windows version from reliable sources like Win32 OpenSSL or Shining Light Productions.
- Verifying SSL Certificates: Once OpenSSL is installed on Windows, you can use similar commands to check SSL certificates as in Linux. The process involves executing commands in the Command Prompt or PowerShell.
- Exploring Windows OpenSSL GUI Tools (Optional): If you prefer a graphical user interface (GUI), several OpenSSL GUI tools are available for Windows. These tools provide a user-friendly way to check SSL certificates and manage cryptographic operations.
SSL Certificate Best Practices and Additional Considerations
To protect sensitive data and preserve trust in online interactions, it is paramount to maintain SSL best practices. Here are some recommended best practices;
- Regular SSL Certificate Maintenance: To ensure a secure online presence, regular SSL certificate maintenance is crucial. Regularly check for certificate expiration dates. Also, monitor certificate revocation status.
- Staying Up-to-Date with OpenSSL: To maintain optimal security, it’s essential to keep OpenSSL installations up to date and stay informed about new releases and security advisories. This will be pivotal in leveraging the latest features and fixes.
- Additional Security Measures: In addition to checking SSL certificates, consider implementing other security measures. Utilize certificate transparency logs, which provide an additional layer of validation. Explore certificate revocation lists (CRLs) and online certificate status protocol (OCSP) checks for real-time certificate validation.
The Bottom Line
Ensuring the security of SSL certificates is a crucial aspect of maintaining a safe online environment. And it doesn’t even matter whether you choose the command-line interface or opt for a GUI tool.
OpenSSL provides the flexibility and functionality needed to bolster your online security. Stay proactive, regularly check SSL certificates, and follow best practices to establish trust and encryption, safeguarding your online interactions.
Writing secure JavaScript code isn’t just about syntax but understanding potential pitfalls and loopholes that can be exploited. Start with comprehensive education about common security risks, including Cross-Site Scripting (XSS) and code injection. Ensure that code is written following best practices such as validating input, sanitizing output, and correctly managing errors.
Consider implementing a linter in your development process to catch issues like the unsafe use of eval() and to enforce style consistency.
Encourage regular peer code reviews; they offer opportunities for learning and catching security issues that automated tools may miss.
Above all, foster a security-focused culture within your development team, where writing secure code becomes second nature.